How Tookitaki AML Solutions Help Philippine E-Wallets Meet Regulations
.svg)
The Philippines has seen a significant surge in the adoption of e-wallets in recent years, driven by increasing smartphone penetration, a growing internet user base, and the demand for convenient digital financial services. In 2017, the number of registered e-wallet accounts in the country was almost 9 million, and by 2020, mobile wallet usage had become three times higher. By 2025, it is expected that the number of e-wallet users will rise to 75.5 million.
E-wallets are transforming the way people in the Philippines make transactions, providing a fast and secure alternative to traditional cash-based payments. This has led to the emergence of numerous e-wallet providers, fueling competition and innovation in the market.
To ensure the safety and security of e-wallet users and maintain the financial system's integrity, the Bangko Sentral ng Pilipinas (BSP) has introduced specific regulations for e-wallet providers under the Electronic Money Institution (EMI) License. These regulations aim to safeguard consumers and mitigate the risks associated with money laundering and terrorist financing. E-wallet providers must comply with these guidelines to obtain and maintain their EMI licenses and operate legally within the country.
Tookitaki's Anti-Money Laundering Suite (AML) solutions can play a vital role in helping e-wallet providers comply with the regulatory requirements under the EMI License in the Philippines. By leveraging advanced technologies and a unique community-based approach, Tookitaki enables e-wallet providers to manage their AML compliance programs effectively. Let's discuss how.
AML Requirements for E-Wallets under the EMI License in the Philippines
AML Requirements for E-Wallets under the EMI License in the Philippines include the following:
A. Customer Due Diligence (CDD) and Enhanced Due Diligence (EDD)
Under the EMI License regulations, e-wallet providers must perform Customer Due Diligence (CDD) on all customers before establishing a business relationship or conducting transactions. CDD involves collecting and verifying customers' identification information, understanding the nature of their business, and determining their risk profile.
{{cta-guide}}
In certain high-risk scenarios, e-wallet providers must conduct Enhanced Due Diligence (EDD) to scrutinize customers and their transactions further. This may involve obtaining additional identification information, verifying the source of funds, and closely monitoring the customer's transaction patterns.
B. Transaction monitoring and reporting
E-wallet providers must implement robust transaction monitoring systems to identify suspicious activities and transactions that may be indicative of money laundering or terrorist financing. This involves setting up appropriate risk-based thresholds and monitoring customer transactions.
E-wallet providers must also report suspicious transactions to the Anti-Money Laundering Council (AMLC) within the stipulated timeframe. Additionally, they must submit covered transaction reports for transactions that meet or exceed the threshold set by the AMLC.
C. Risk assessment and management
E-wallet providers must conduct regular risk assessments to identify, evaluate, and mitigate the risks associated with money laundering and terrorist financing. This involves considering various factors such as customer profiles, products and services offered, delivery channels, and geographic locations. Based on the risk assessment findings, e-wallet providers should develop and implement appropriate risk management measures for achieving holistic risk coverage.
D. Record-keeping
E-wallet providers must maintain comprehensive records of customer identification documents, transaction details, and other relevant information for at least five years. These records must be readily available for inspection by the BSP or AMLC upon request.
E. Compliance program and training
E-wallet providers must establish a comprehensive AML compliance program that includes appointing a Compliance Officer, developing internal policies and procedures, and regular employee training. The compliance program should be tailored to the specific risks faced by the e-wallet provider and be regularly reviewed and updated to ensure its effectiveness.
By adhering to these AML requirements, e-wallet providers can demonstrate their commitment to maintaining a secure and compliant environment, ultimately contributing to the integrity of the Philippines' financial ecosystem.
An Overview of Tookitaki's AML Compliance Offerings
Tookitaki is a pioneer in the fight against financial crime, leveraging a unique and innovative approach that transcends traditional solutions. The company's Anti-Money Laundering Suite (AMLS) and Anti-Financial Crime (AFC) Ecosystem work in tandem to address the limitations of siloed systems in combating money laundering. The AFC Ecosystem is a community-based platform that facilitates sharing of information and best practices in the battle against financial crime. Powering this ecosystem is the Typology Repository, a living database of money laundering techniques and schemes. This repository is enriched by the collective experiences and knowledge of financial institutions, regulatory bodies, and risk consultants worldwide, encompassing a broad range of typologies from traditional methods to emerging trends.
The AMLS is a software solution deployed at financial institutions. It is an end-to-end operating system that modernises compliance processes for banks and fintechs. The AMLS collaborates with the AFC Ecosystem through federated machine learning. This integration allows the AMLS to extract new typologies from the AFC Ecosystem, executing them at the clients' end to ensure that their AML programs remain cutting-edge.
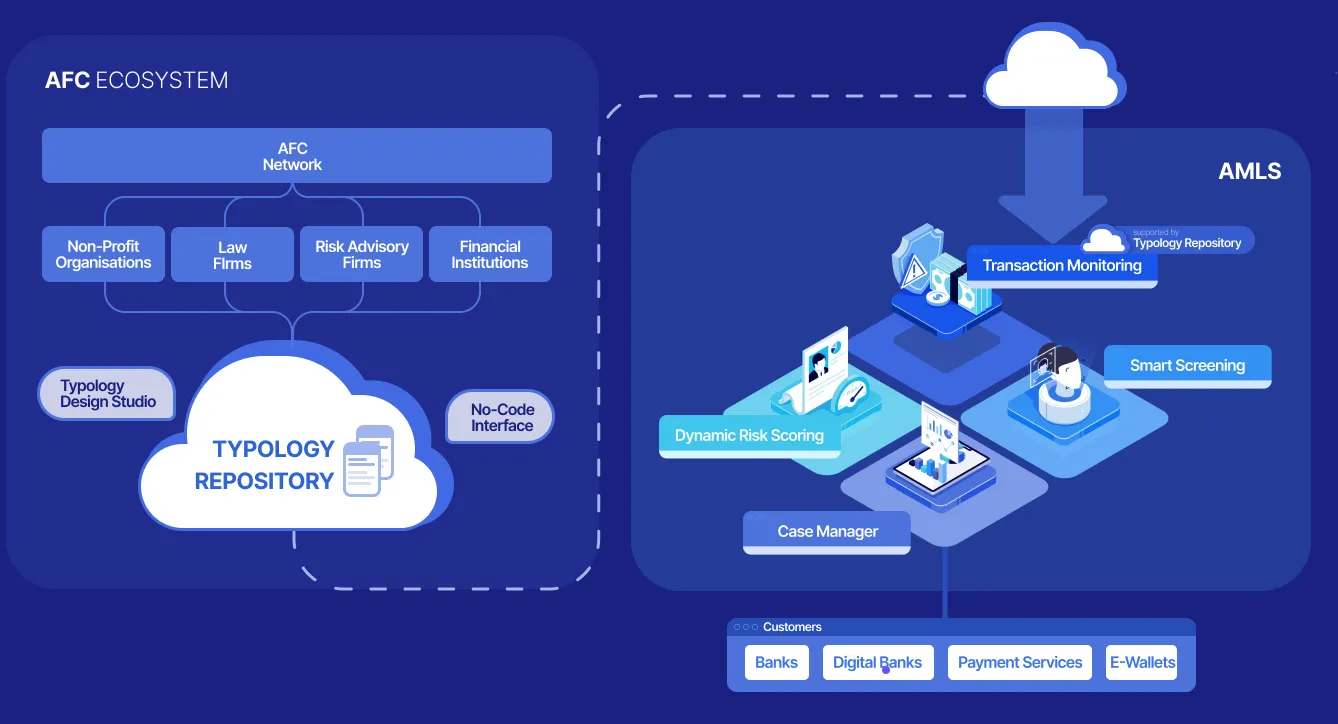
Tookitaki's Anti-Money Laundering Suite (AMLS) and Anti-Financial Crime (AFC) Ecosystem are designed to help e-wallet providers and other financial institutions comply with AML regulations, minimize financial crime risks, and improve their operational efficiency. By leveraging advanced technologies and a community-based approach, Tookitaki's solutions can effectively detect and prevent suspicious activities while streamlining compliance processes.
By implementing Tookitaki's AML solutions, e-wallet providers can stay ahead of regulatory changes, mitigate risks, and focus on their core business operations, ultimately contributing to a safer and more secure financial ecosystem in the Philippines.
AMLS Modules
Tookitaki's AMLS consists of several modules that address specific AML compliance requirements, including:
- Transaction Monitoring: The Transaction Monitoring module is designed to detect suspicious patterns of financial transactions that may indicate money laundering or other financial crimes. It utilises powerful simulation modes for automated threshold tuning, allowing AML teams to focus on the most relevant alerts and improve their efficiency. The module also includes a built-in sandbox environment, which allows financial institutions to test and deploy new typologies in a matter of minutes.
- Smart Screening: The Smart Screening module screens prospects, customers and counterparties to detect potential matches against sanctions lists, PEPs, and other watchlists. It includes 50+ name-matching techniques and supports multiple attributes such as name, address, gender, date of birth, and date of incorporation. It covers 20+ languages and ten different scripts and includes a built-in transliteration engine for effective cross-lingual matching. This module is highly configurable, allowing it to be tailored to the specific needs of each financial institution.
- Dynamic Risk Scoring: The Customer Risk Scoring solution is a flexible and scalable prospect and customer risk ranking program that adapts to changing customer behaviour and compliance requirements. Powered by advanced machine learning, this module creates a dynamic, 360-degree risk profile of customers.
- Case Manager: The Case Manager provides compliance teams with the platform to collaborate on cases and work seamlessly across teams. It comes with a host of automation built to empower investigations and regulatory reporting. Financial institutions can configure the Case Manager to automate processes such as case creation, allocation, data gathering, and so on, allowing investigators to become more effective.
Benefits of AMLS and AFC Ecosystem
By making use of Tookitaki's AMLS and AFC Ecosystem, e-wallet providers in the Philippines can benefit from the following:
- Comprehensive Typology Repository: By fostering collaboration between financial institutions, regulatory bodies, and risk consultants, Tookitaki's AFC Ecosystem creates a collective knowledge base through the Typology Repository. This living database contains up-to-date money laundering techniques and schemes, which enables financial institutions to stay informed about emerging trends and threats.
- Enhanced Detection Accuracy: Financial institutions can better identify suspicious activities and potential money laundering risks with access to the latest typologies and schemes. This leads to improved detection accuracy and a more robust AML program.
- Reduction in False Alerts: Tookitaki's innovative technology, combined with the insights from the AFC Ecosystem, helps to minimize false positives. By accurately identifying suspicious activities, financial institutions can focus their resources on high-risk cases and reduce the operational burden of false alerts.
- Adaptive Learning: Federated machine learning enables Tookitaki's AMLS to continuously learn from the AFC Ecosystem, ensuring that the AML program remains adaptive and up-to-date with the latest trends and regulatory changes.
- Streamlined Compliance Processes: Tookitaki's AMLS modernizes compliance processes, making them more efficient and effective. This results in faster response times and allows financial institutions to maintain compliance with evolving regulations.
- Improved Collaboration: The community-based approach encourages knowledge sharing and best practices among financial institutions, regulatory bodies, and risk consultants, fostering a cooperative environment in the fight against financial crime.
How Tookitaki's AML Solutions Address the EMI License Requirements
Tookitaki's advanced features enable e-wallet providers to manage compliance effectively, mitigate risks, and maintain operational efficiency. The AMLS ensures robust Customer Due Diligence (CDD) and Enhanced Due Diligence (EDD) processes with its Smart Screening and Dynamic Risk Scoring modules, ensuring that e-wallet providers comply with their regulatory obligations. By conducting thorough screening on customers and monitoring their ongoing risk profiles, the AMLS helps e-wallet providers identify potential high-risk customers and manage their risk exposure more effectively.
The Transaction Monitoring module, powered by the Typology Repository, analyzes customer transactions, identifies unusual patterns, and generates alerts for potentially suspicious transactions. This enables e-wallet providers to detect and prevent money laundering and terrorist financing activities more effectively.
The Dynamic Risk Scoring module helps e-wallet providers evaluate their overall AML risk exposure, identify potential vulnerabilities, and implement effective risk mitigation measures. By continuously monitoring and assessing risk factors, the AMLS enables e-wallet providers to adapt their risk management strategies as needed, ensuring ongoing compliance and reducing the likelihood of regulatory penalties.
Furthermore, Tookitaki's Case Manager simplifies the reporting process, making it easier for e-wallet providers to submit timely and accurate reports to regulatory authorities. Tookitaki also assists e-wallet providers in maintaining accurate and up-to-date records of customer information, transactions, and risk assessments, as required by the EMI License regulations. By providing comprehensive tools and resources, Tookitaki's AMLS helps e-wallet providers ensure that their compliance programs are effective, efficient, and in line with regulatory requirements.
The Future of AML Compliance for E-Wallets in the Philippines
As e-wallets continue to grow in popularity, it is crucial for these providers to have robust AML solutions in place to meet the regulatory requirements under the Electronic Money Institution (EMI) License in the Philippines. Implementing effective AML compliance measures helps e-wallets avoid potential penalties and contributes to a safer and more transparent financial ecosystem. Tookitaki's comprehensive AML platforms, the AMLS and the AFC Ecosystem, have been designed to help e-wallet providers meet their regulatory obligations effectively. They empower e-wallets to streamline their compliance processes, manage risks, and maintain operational efficiency.
We encourage interested parties to book a demo to fully understand the benefits of Tookitaki's AML solutions and how they can help e-wallet providers achieve compliance and mitigate risks. By experiencing Tookitaki's offerings firsthand, e-wallet providers can gain valuable insights into how these solutions can transform their compliance processes, reduce risks, and contribute to the success of their business in the rapidly evolving digital payments landscape.
Experience the most intelligent AML and fraud prevention platform
Experience the most intelligent AML and fraud prevention platform
Experience the most intelligent AML and fraud prevention platform
Top AML Scenarios in ASEAN

The Role of AML Software in Compliance




.png)





