E-wallets in Singapore: How Tookitaki Helps Ensure Secure Onboarding
.svg)
In recent years, e-wallets have gained significant traction in Singapore, revolutionizing how people make payments and manage their finances. As a convenient, cashless, and efficient mode of payment, e-wallets have transformed the financial landscape, providing users with a seamless experience for both online and offline transactions. The growth of e-wallets in Singapore can be attributed to the country's high smartphone penetration, tech-savvy population, and the government's push towards a cashless society.
With the increasing adoption of e-wallets, secure onboarding of users has become a critical aspect for providers to ensure a safe and trustworthy experience. As e-wallets store sensitive financial information, onboarding must adhere to stringent regulatory requirements, including anti-money laundering (AML) and know-your-customer (KYC) checks. This is where Tookitaki comes into play, offering innovative solutions that enable e-wallet providers to streamline their onboarding processes while maintaining the highest levels of security and compliance.
The E-wallet Landscape in Singapore
The rise of e-wallet usage in Singapore has been nothing short of remarkable. The e-wallet landscape in Singapore has been growing rapidly, with the country aiming to become a cashless society and reduce the use of cheques by 2025. This surge in popularity can be attributed to the country's robust digital infrastructure, supportive government policies, and an increasingly tech-savvy population. As a result, e-wallets have become an integral part of Singapore's drive towards becoming a Smart Nation, with the aim of creating a cashless, digital economy.
These e-wallets offer various capabilities, such as peer-to-peer transfers, bill payments, online shopping, and contactless payments at retail outlets, making them an attractive option for consumers seeking a convenient and efficient payment solution.
Several key players have emerged in the Singapore e-wallet market, offering a range of services and features to cater to the diverse needs of consumers and businesses. Some of the most prominent e-wallet providers include GrabPay, PayLah!, PayAnyone, FavePay, and Alipay. These e-wallets offer various capabilities, such as peer-to-peer transfers, bill payments, online shopping, and contactless payments at retail outlets, making them an attractive option for consumers seeking a convenient and efficient payment solution.
Several factors have contributed to the growth of e-wallets in Singapore.
- Firstly, the high smartphone penetration rate and widespread internet access have provided the necessary infrastructure for e-wallet adoption.
- Secondly, the government's push for a cashless society, through initiatives such as the Unified Point of Sale (UPOS) system and the introduction of the Singapore Quick Response Code (SGQR), has further encouraged the use of e-wallets.
- Thirdly, the growing trend of online shopping and the demand for contactless payments, particularly in the wake of the COVID-19 pandemic, have accelerated the adoption of e-wallets as a preferred mode of payment.
{{cta-guide}}
Money Laundering Risks Related to E-wallets
While e-money and e-wallets offer numerous benefits, they also carry significant money laundering risks. E-wallets, as online storage systems holding users' banking information for payment purposes, have seen significant growth since 2017, leading to a rise in money laundering concerns. The money laundering risk associated with e-money was assessed as medium, and the terrorist financing risk as low, according to the National Risk Assessment (NRA) 2015. However, the NRA 2017 revised the terrorist financing risk to a medium rating. Open-loop prepaid cards, a form of e-money, were recognized as potentially high risk.
Investigations have linked electronic money institutions (EMIs), which can issue pre-paid payment cards or digital wallets, to money laundering, fraud, and other financial crimes. To mitigate these risks, financial institutions are encouraged to develop a rigorous and comprehensive risk management process that addresses the known material risks and accommodates changes in the type and intensity of material risks associated with electronic banking and e-money activities.
Financial regulators worldwide have developed guidance and regulations to mitigate these risks and ensure the safety and security of digital payment systems. Providers of e-money issuance services under the Payment Services Act 2019 are subject to anti-money laundering (AML) and countering financing of terrorism (CFT) risk mitigation measures. These measures aim to address user protection, interoperability, and technology and cyber security risks associated with e-wallets.
Read More: Streamlining Compliance with AML Onboarding Software
The Importance of Secure Onboarding
As the e-wallet landscape in Singapore continues to grow, it becomes increasingly important for e-wallet providers to adhere to strict Anti-Money Laundering (AML) regulatory requirements. These regulations aim to prevent financial crimes such as money laundering, terrorist financing, and fraud associated with digitalising financial services.
E-wallet providers must comply with AML regulations set by the Monetary Authority of Singapore (MAS) and other relevant authorities. Compliance with these regulations helps e-wallet providers identify and manage potential AML risks associated with their services. Some potential AML risks associated with e-wallet usage include the anonymity of digital transactions, the speed of fund transfers, and the cross-border nature of these transactions, which criminals can exploit for money laundering and other illicit activities.
To ensure user trust and security, e-wallet providers must implement secure customer onboarding processes. This typically involves Know Your Customer (KYC) checks, which are essential for verifying the identity of users and assessing the risk they may pose. KYC checks include collecting and verifying user information such as name, date of birth, address, and identification documents. These checks help e-wallet providers to detect and prevent potential financial crimes, thus ensuring a secure and trustworthy environment for their users.
By adhering to AML regulatory requirements and implementing secure onboarding processes, e-wallet providers in Singapore can effectively mitigate risks, protect their customers, and build trust in their services. This, in turn, will contribute to the continued growth and success of the e-wallet landscape in the country.
Tookitaki's Role in Ensuring AML Compliance for E-wallets
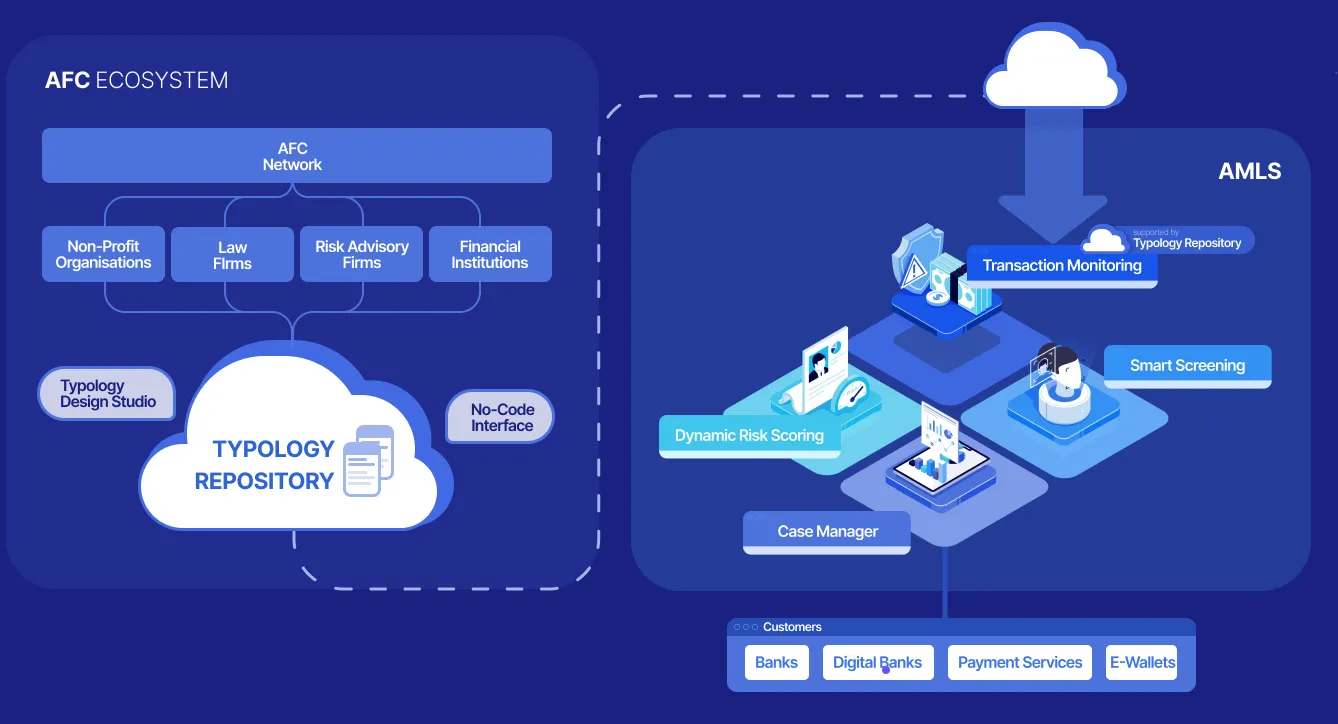
Tookitaki is a pioneer in the fight against financial crime, leveraging a unique and innovative approach that transcends traditional solutions. The company's Anti-Money Laundering Suite (AMLS) and Anti-Financial Crime (AFC) Ecosystem work in tandem to address the limitations of siloed systems in combating money laundering.
The AFC Ecosystem is a community-based platform that facilitates sharing of information and best practices in the battle against financial crime. Powering this ecosystem is our Typology Repository, a living database of money laundering techniques and schemes. This repository is enriched by the collective experiences and knowledge of financial institutions, regulatory bodies, and risk consultants worldwide, encompassing a broad range of typologies from traditional methods to emerging trends.
The AMLS is a software solution deployed at financial institutions. It is an end-to-end operating system that modernises compliance processes for banks and fintechs. The AMLS collaborates with the AFC Ecosystem through federated machine learning. This integration allows the AMLS to extract new typologies from the AFC Ecosystem, executing them at the clients' end to ensure that their AML programs remain cutting-edge.
How Tookitaki's technology addresses the compliance challenges of e-wallets
Tookitaki's technology goes beyond traditional rule-based systems by utilizing machine learning algorithms to identify and predict financial crime patterns. This enables e-wallet providers to detect suspicious activities more accurately and effectively while reducing false positives. The technology also automates the KYC process, streamlining the onboarding experience for both the provider and the user.
By implementing Tookitaki's AML compliance solutions, e-wallet providers can enjoy several benefits, including:
- Improved regulatory compliance: Tookitaki's solutions ensure that e-wallet providers remain compliant with AML regulations, reducing the risk of fines and reputational damage.
- Enhanced risk management: The advanced analytics capabilities of Tookitaki's technology help e-wallet providers to identify better and manage potential risks associated with their services.
- Increased operational efficiency: Automating the KYC process and other compliance tasks leads to cost savings and improved operational efficiency.
- Greater customer trust: Secure onboarding processes, coupled with robust AML measures, contribute to building user trust and confidence in the e-wallet provider's services.
Implementing Tookitaki's AMLS positively impacts the onboarding process and user experience for e-wallet providers in several ways:
- Streamlined onboarding: Tookitaki's real-time prospect screening and prospect risk scoring solutions help mitigate AML risks while onboarding new customers, providing a faster and more seamless experience.
- Enhanced security: The AMLS help de-risk business with a 360-degree dynamic risk view of customers. Its integrated transaction monitoring, smart screening, customer risk scoring and case management modules provide fast-growing e-wallets complete control of their AML risks.
- Reduced friction: By minimizing false positives and automating compliance tasks, Tookitaki's solutions help reduce friction in the onboarding process, leading to increased user satisfaction.
Tookitaki plays a crucial role in ensuring secure onboarding for e-wallet providers in Singapore by offering cutting-edge AML compliance solutions. These solutions not only help providers adhere to regulatory requirements but also enhance their risk management capabilities, improve operational efficiency, and foster trust among users.
Securing the Future of E-wallets in Singapore
As the e-wallet market continues to grow in Singapore, the significance of secure onboarding cannot be overstated. It plays a vital role in safeguarding users' personal and financial information while ensuring compliance with AML regulations. To maintain the trust of users and regulators alike, e-wallet providers must prioritize the adoption of advanced AML compliance solutions like Tookitaki's.
Tookitaki's innovative solutions provide enhanced security and compliance measures that help e-wallet providers stay ahead in a competitive market while ensuring a seamless user experience. By implementing Tookitaki's AML compliance technology, e-wallet providers can effectively mitigate risks, streamline their onboarding processes, and foster trust among their users.
Don't miss the opportunity to strengthen your e-wallet's security and compliance measures. Book a demo for Tookitaki’s AML compliance solutions today and experience the difference that cutting-edge technology can make in securing the future of e-wallets in Singapore.
Experience the most intelligent AML and fraud prevention platform
Experience the most intelligent AML and fraud prevention platform
Experience the most intelligent AML and fraud prevention platform
Top AML Scenarios in ASEAN

The Role of AML Software in Compliance




.png)





